Setting Up A Virtual Machine Hacking Lab
Virtual Machines form the backbone of AWS and many other services in the industry, but that is not the point of this article. The point of this article is to help you set up a method for you to play around with hacking into things. You will need enough ram to run 2 machines at once if you're gonna do this. Without further ado, let's get started.
Installing Virtualbox and Getting Your Machines
Virtualbox is the software we'll be doing this with. It can be downloaded here. Run the program and install Virtualbox.
We'll need a pre-built virtual machine for both an attacker and a defender. You have options for both these things.
Some prominent hacking distributions of Linux that you can use for your hacking lab are:
For systems to attack, the best one is probably Metasploitable, because its preloaded with vulnerabilities, but you can always configure your own system to be vulnerable and try to break into it. A good resource if you do this would be STIGs, which are step by step guides of how to harden a system with default settings.
Setting Up A Network
In order to test out vulnerabilities in software, you must first configure your virtual machines in such a way that they can talk to each other. This involves setting up an internal network of virtual machines with DHCP (Dynamic Host Configuration Protocol). DHCP is what gives us an IP address when we connect to something like a router.
There is an option to do it without DHCP and assign IP addresses manually, but that would be an extra step, and any time you use a new machine you'd have to configure it so that it has an IP address.
Setting up a DHCP network is easy. It's one command in the command prompt:
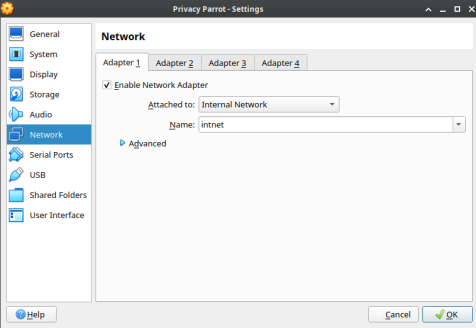
VBoxManage dhcpserver add --netname intnet --ip 10.0.2.0 --netmask 255.255.255.0 --lowerip 10.0.2.2 --upperip 10.0.2.254 --enable
This adds DHCP to the virtual network known as intnet. The "10.0.2.0" and "255.255.255.0" specifies the subnet 10.0.2.0 as the network. Lowerip and upperip specify the range of addresses to assign. Finally, enable says to enable it.
Attaching Network To A VM
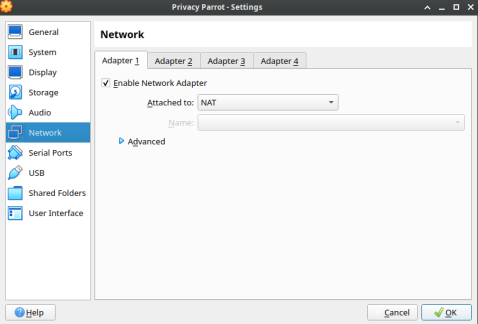
- Head to Network Settings for the VM.
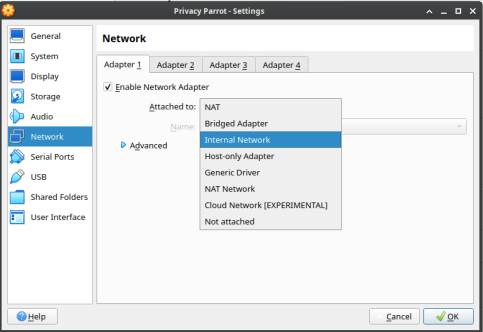
- Select Internal Network.
- Put in the name of the internal network.
It is worth noting if this is the only network adapter you attach, you won't be able to reach the internet. You will need to attach a separate NAT adapter if you want to be able to reach the internet.
Happy Hacking
Enjoy your machine lab. Now that you got it set up, you have a place to practice hacking skills.
Caution: It is worth noting that something like Metaspoitable should not be connected to the internet via a secondary NAT adapter as it is vulnerable. You can connect your other target machines to the internet, as the likelihood of machines that are still being supported being exceedingly vulnerable without the user configuring them that way is small.
If you are feeling a little more adventurous, you can also quarantine a VM and load it full of malware to get an idea of what the malware is doing. Be careful though.